Cloudflare published its 2026 Threat Report on 3 March 2026, and the headline number is hard to ignore: 94% of all login attempts across its global network are bots. Not humans. Not customers. Automated scripts hammering login forms with stolen credentials, brute-force guesses, and stuffed password lists.
The report draws from Cloudflare's position as a reverse proxy for roughly 20% of all websites, processing 79 million HTTP requests per second at peak. The company says it blocks 230 billion threats per day. When you're looking at traffic at that scale, the patterns carry weight. And the patterns in 2025 were bleak.
Stolen Credentials Are the Real Problem

The bot traffic stat grabs attention, but dig into the 6% of logins that are actually human and it gets worse. Of those human logins, 46% used credentials already found in known data breaches. Nearly half of all real people logging into websites are using passwords that attackers already have.
This links directly to ransomware. Cloudflare's Cloudforce One threat intelligence team traced 54% of ransomware incidents in 2025 back to infostealer malware, which harvests saved passwords from browsers, password managers, and system keychains. Stolen credentials get sold in bulk on dark web markets. Buyers use them to access business accounts, email systems, hosting control panels, and WordPress admin dashboards.
"Threat actors are constantly changing tactics, finding new vulnerabilities to exploit and ways to overwhelm their victims. To avoid being caught off guard, organizations must shift from a reactive posture to one fueled by real-time, actionable intelligence."
Blake Darché, Head of Threat Intelligence, Cloudforce One
For a UK small business running a WordPress site, "reactive posture" means waiting until your hosting provider emails you about suspicious logins. A proactive posture means enforcing two-factor authentication, using unique passwords for every service, and checking whether your credentials have already leaked. Our coverage of February's critical WordPress plugin vulnerabilities showed how quickly attackers exploit known weaknesses. Leaked credentials make the problem worse by orders of magnitude.
DDoS Attacks Doubled in 2025

Cloudflare mitigated 47.1 million DDoS attacks in 2025, double the 2024 figure. The biggest single attack hit 31.4 Tbps in November 2025, attributed to the Aisuru botnet. Hyper-volumetric attacks (those exceeding 1 Tbps) grew 700% year on year.
Most attacks lasted under 10 minutes. That's deliberate. Short bursts are harder to detect and respond to manually. By the time someone notices the traffic spike, the damage is done and the attacker has moved on. For businesses without automated DDoS mitigation, a 10-minute burst is enough to take a site offline, lose sales, and frustrate customers who won't try again later.
"Hackers thrive on the gaps left by fragmented, stale threat intelligence. At Cloudflare, we've built the largest and most comprehensive global sensor network that gives us a front-row seat to threats invisible to everyone else."
Matthew Prince, Co-founder and CEO, Cloudflare
Prince's comment underlines why platform-level protection matters. Individual businesses can't build their own threat intelligence networks. They rely on hosting providers and CDNs to absorb and filter malicious traffic before it hits the server. When we saw the Cloudflare outage in January 2026, it was a reminder of just how much web infrastructure depends on these intermediary layers.
Email Authentication Is Failing at Scale

The report analysed 450 million emails. The results: 46% failed DMARC authentication, 43% failed SPF checks, and 44% lacked valid DKIM signatures. These three protocols are the backbone of email security. They prove that an email genuinely came from the domain it claims to come from. When nearly half of all emails fail these checks, phishing and business email compromise become trivially easy.
Cloudflare intercepted $123 million in BEC theft attempts during the reporting period, averaging $49,225 per attempt. The top brands impersonated in phishing attacks were Windows, SANS, Microsoft, Stripe, and Facebook.
If you haven't configured SPF, DKIM, and DMARC records for your business domain, you're leaving the door open. Our free DNS Lookup tool shows you exactly what DNS records your domain has right now. And our DNS records guide walks through setting them up correctly.
What This Means for Your Business
The 94% bot login stat has a practical translation for UK business owners. If your WordPress site has a /wp-admin/ login page, it's being hit by automated attacks. Not maybe. Every day. The question is whether your defences hold. You can scan your WordPress site's security in 30 seconds with our free tool to see exactly what's exposed.
Here's what to check this week:
- Enable two-factor authentication on your WordPress admin, hosting control panel, and email accounts. Password-only login isn't safe when 46% of human logins use compromised credentials.
- Check for credential leaks at haveibeenpwned.com. If your email address appears in a breach database, change every password linked to it. Use a password manager to generate unique passwords for each service.
- Verify your email authentication with our DNS Lookup tool. Search for your domain and check for SPF, DKIM, and DMARC records. Missing records mean anyone can send emails pretending to be your business.
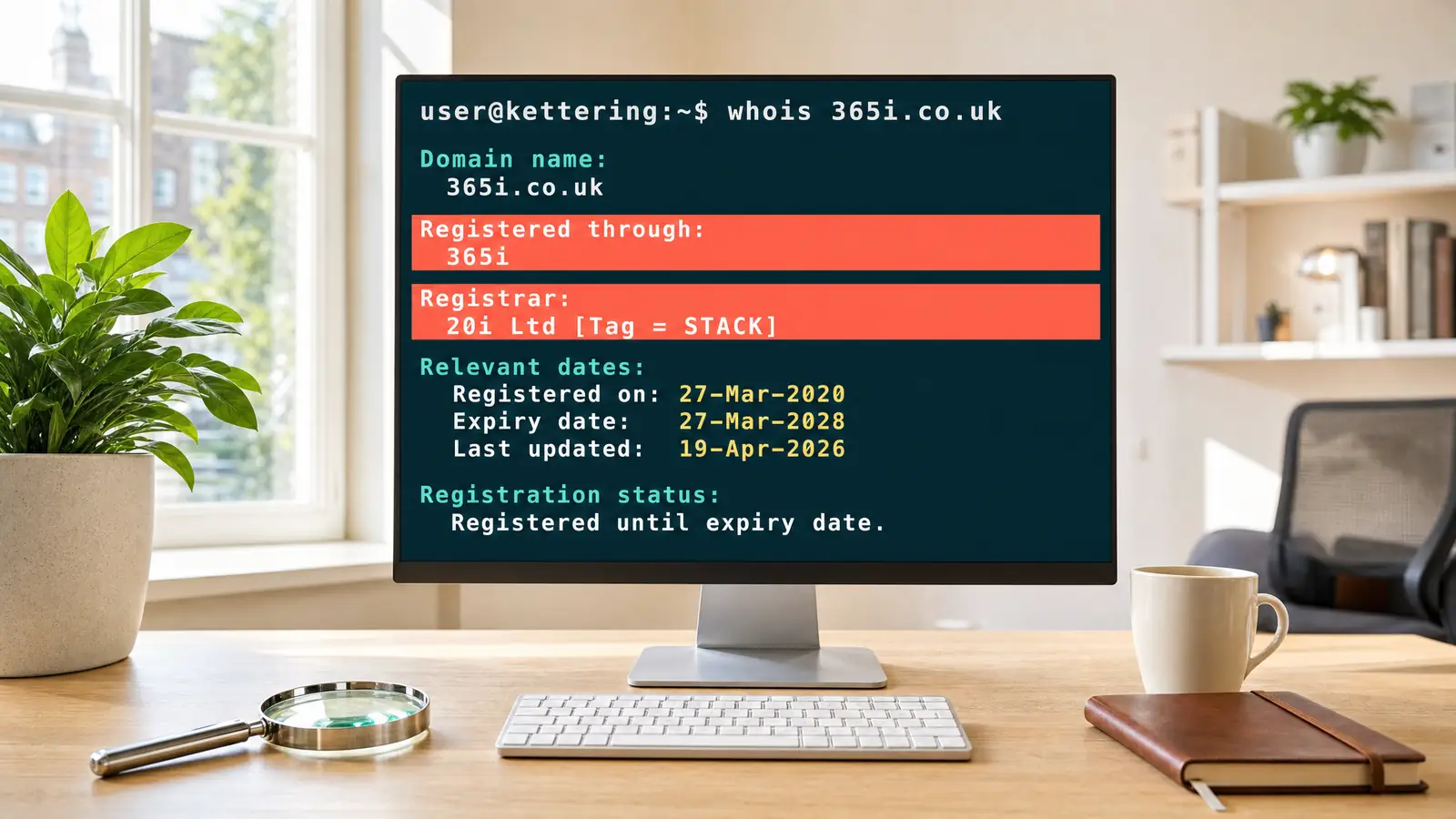
- Review your hosting security. Does your provider include DDoS protection, a web application firewall, and brute-force login protection? 365i's secure hosting platform includes all three as standard on every plan.
- Keep WordPress and plugins updated. Cloudflare found that most web application attacks in 2025 targeted known vulnerabilities where patches already existed. Running outdated software is an open invitation. Our WordPress security and GDPR checklist covers what to prioritise.
The web design perspective matters here too. If you build or maintain sites for clients, this report should inform your security baseline. As our sister site explored in its Google threat intelligence coverage, AI-powered malware is accelerating the speed at which attackers find and exploit vulnerable sites.
Who's Behind the Attacks
Cloudflare's Cloudforce One team tracked several nation-state threat actors through the period. The report names five groups using internal codenames: FrumpyToad and PunyToad (China), NastyShrew (Russia), PatheticSlug (North Korea), and CrustyKrill (Iran). While these groups primarily target government and enterprise infrastructure, the tools and techniques they develop filter down to criminal groups that go after smaller businesses.
The report also disclosed CVE-2026-22813, a CVSS 9.4 severity vulnerability in a widely used markdown rendering pipeline that Cloudflare discovered and patched. High-severity CVEs like this one show why platform-level patching matters: businesses using affected software through their hosting provider get protected as soon as the provider patches, without needing to take any action.
What to Watch Next
Cloudflare's data shows a clear trajectory: attacks are getting faster, more automated, and more reliant on credentials stolen from previous breaches. The 10-minute DDoS window suggests attackers are optimising for speed over duration. Bot login rates will only climb as credential databases grow and AI makes automated attacks cheaper to run.
For UK businesses, the priority hasn't changed. Get the basics right: strong unique passwords, two-factor authentication, current software, and properly configured SSL certificates. Use security header checks to verify your server is hardened. And pick a hosting provider that treats security as a platform feature, not an optional extra.
Frequently Asked Questions
How many login attempts are bots according to Cloudflare's 2026 report?
94% of all login attempts across Cloudflare's global network in 2025 were automated bots. Only 6% came from actual humans. The bots use credential stuffing, brute-force attacks, and stolen password lists to attempt access to websites, applications, and APIs.
What percentage of human logins use compromised credentials?
46% of the human login attempts Cloudflare observed used credentials already found in known data breach databases. This means nearly half of real users are logging in with passwords that attackers already possess, making credential stuffing attacks highly effective.
How many DDoS attacks did Cloudflare mitigate in 2025?
47.1 million DDoS attacks in 2025, exactly double the 2024 figure. Hyper-volumetric attacks exceeding 1 Tbps grew 700% year on year. The largest single attack reached 31.4 Tbps in November 2025, attributed to the Aisuru botnet.
Does this affect WordPress sites specifically?
Yes. WordPress powers over 40% of all websites, making it the most targeted CMS. The /wp-admin/ and /wp-login.php endpoints are hit by automated bot traffic constantly. Two-factor authentication, strong passwords, and keeping plugins updated are the most effective defences for WordPress site owners.
What email authentication records do I need?
Three records: SPF (Sender Policy Framework), DKIM (DomainKeys Identified Mail), and DMARC (Domain-based Message Authentication, Reporting, and Conformance). Together they verify that emails from your domain are genuine and haven't been spoofed. Without them, attackers can send emails pretending to be your business. You can check your current setup with a DNS Lookup tool.
How can I check if my credentials have been leaked?
Visit haveibeenpwned.com and enter your email address. The site checks whether your email appears in known data breach databases. If it does, change your password immediately on every service that uses that email. Use a password manager to generate unique passwords, and enable two-factor authentication wherever available.
What is credential stuffing?
Credential stuffing is an automated attack where bots take username/password pairs leaked from one data breach and try them on thousands of other websites. It works because people reuse passwords. If your email and password leaked from one service, attackers will try that same combination on WordPress, email, banking, and hosting login pages.
How can a small business protect against DDoS attacks?
Choose a hosting provider with built-in DDoS mitigation at the platform level. Individual businesses can't absorb volumetric attacks on their own. Platform-level protection filters malicious traffic before it reaches your server, so your site stays online even during an attack. 365i's hosting platform includes DDoS protection on every plan.
Don't wait for an attack to find out your site isn't protected
Every 365i hosting plan includes DDoS protection, a web application firewall, and brute-force login defence as standard. Your site's security shouldn't depend on which plan you chose.
Explore Secure HostingSources
- Introducing the 2026 Cloudflare Threat Report - Cloudflare Blog
- Cloudflare 2026 Threat Intelligence Report - Cloudflare Press Release
- Cloudflare tracked 230 billion daily threats and here is what it found - Help Net Security
- Cloudflare warns AI and SaaS integrations are fueling industrial-scale cybercrime - SiliconANGLE
Published: · Last reviewed: · Written by: Mark McNeece, Founder & Managing Director, 365i
Editorially reviewed by: Mark McNeece on · Our editorial standards